

Makes sense now, thank you


Makes sense now, thank you


instead of in an encrypted format on its internal systems.
Riiight, like that’s any better. Jokes aside, it’s hard to imagine what kind of “mistake” results in storing plain text instead of hashing, unless the mistake was in choosing whoever made the security assessment


Notthebees


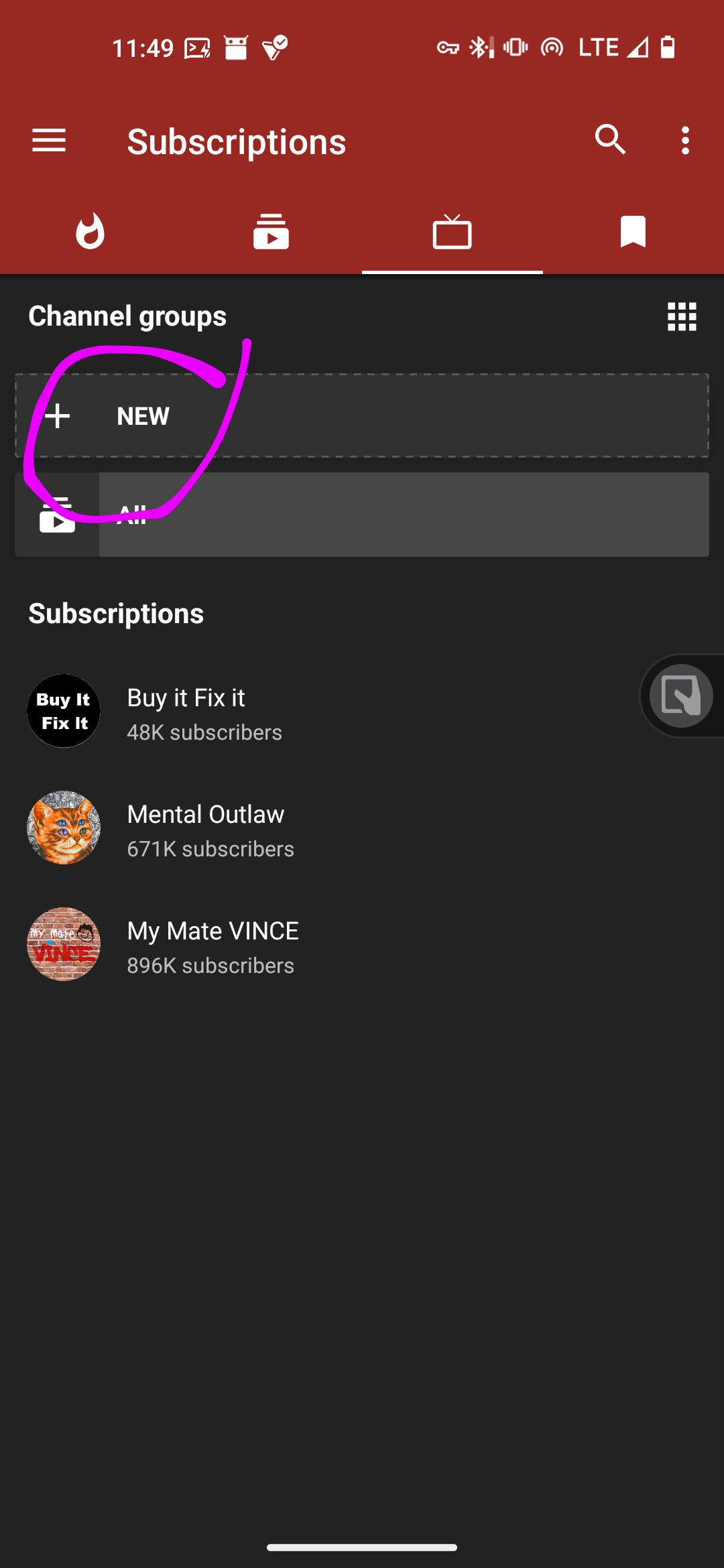
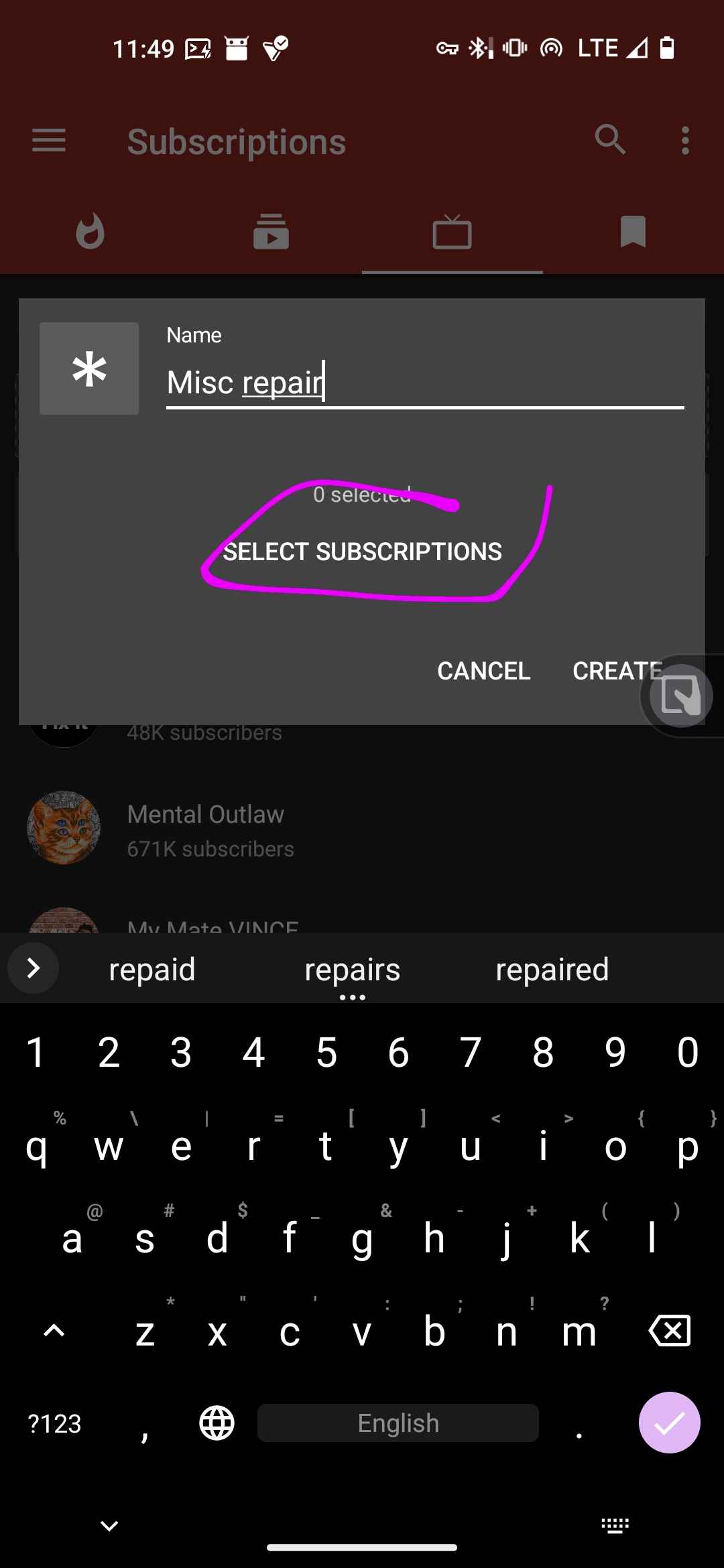
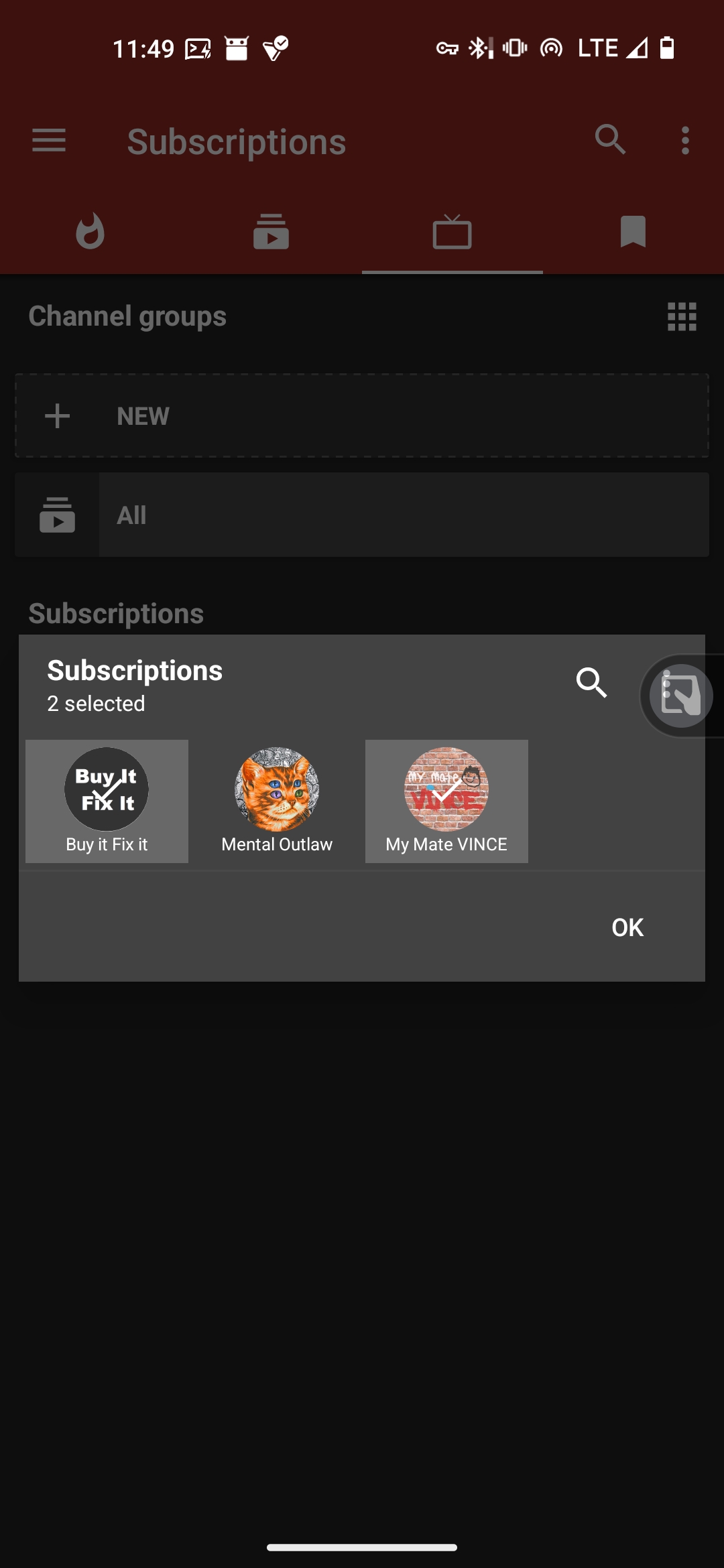
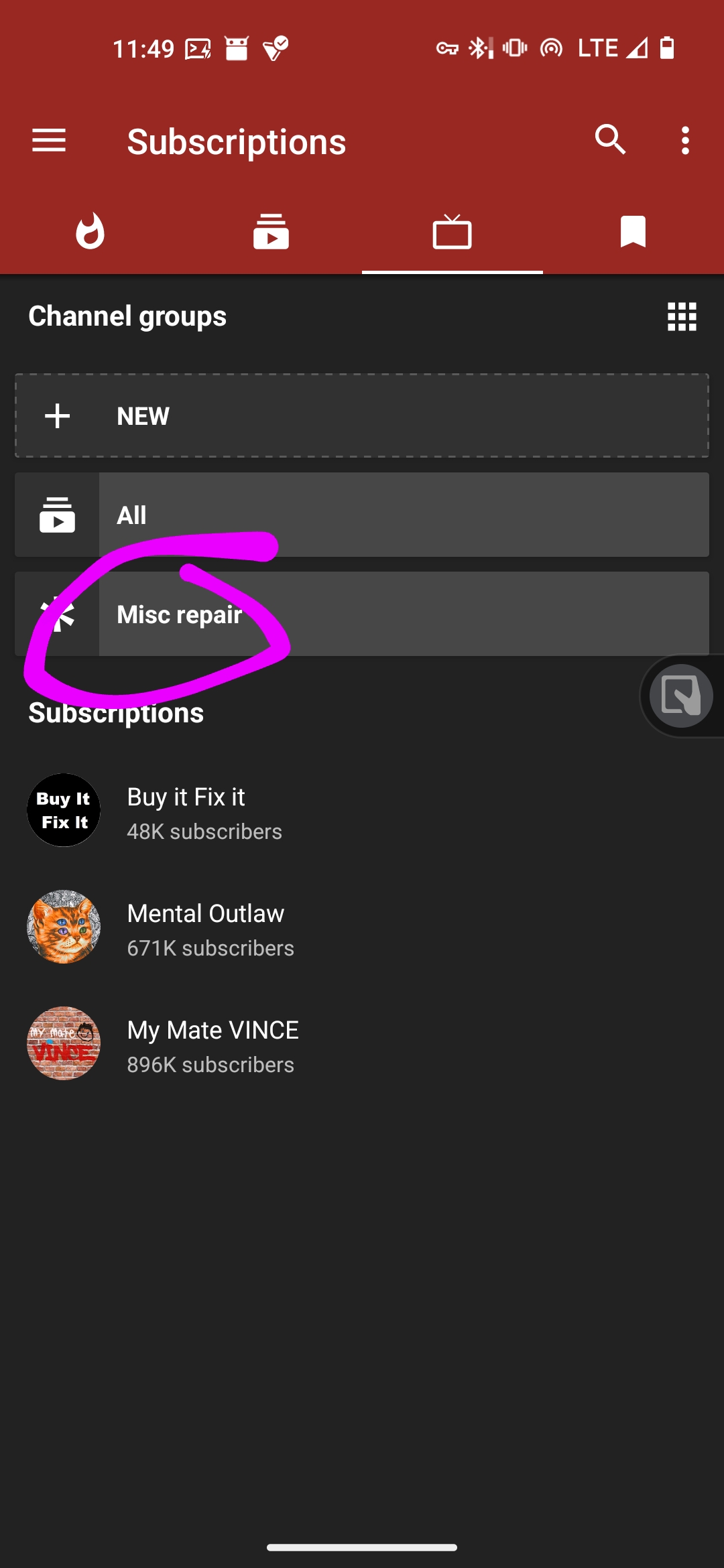
Well, newpipe has channel groups for quite a while now.


it used to be “see source, but no touch source” when it came out, and now it’s “see source, touch source, no sell source”. Not exactly proprietary, not free as in freedom. Kinda gray zone here, pun intended
Plot twist: they code in replit or smth like that


Probably some scientific theory on not letting s3 buckets eat all your money /jk


[Removed]


I guess you should use proxmox at this point 🤣
Well, I’ve heard of at least one case where a PD charder likely died in a way that the output voltage was consistently above 5. Not sure what exactly, but it managed to fry a laptop via type-c that didn’t support charging, and 5v won’t do that.
App pinning has an explicit warning that “personal data may be accessible” and “pinned apps may open other apps”. I mean, it’s better than nothing, but I’d prefer not to rely on it anyways.


They’ve explicitly told in there FAQ 0 bytes of info was disclosed. And I suspect whatever they’ve shared with Germans alone wasn’t 7 bits long.


Soo, how exactly CC solves the issue? I suspect it wouldn’t stop those who ignored a much more lax GPL, tbh


It’s not like they exactly didn’t before: https://www.androidpolice.com/telegram-germany-user-data-surrendered/
Also, nothing said about whether they’re going to start making transparency reports, not that I’ve expected anything else from this crapshow of a messenger…
If you want something like graphene or calyx (I.e. with additional de-googling and security improvements), take a look at DivestOS: https://divestos.org/pages/devices#device-blueline
Crdroid (which claims performance improvements, but also has a lot of customization options; reminds me of now deceased resurrection remix) is also good but doesn’t seem to officially support your device. There may be some ports on XDA, tho.
You’re probably looking for these 2
They’re more secure (albeit in many wsys security through obscurity) than private, although the privacy aspect is probably among the best you can get by default as far as I can tell. On the other hand, if you’re willing to do some relatively simple steps and buy specific hardware, you can achieve better privacy and security on both mobile (graphene) and desktop (qubes) devices.
I personally dislike them for building unrepareable crap, tho.
Depends on your definition of “what”, and the server you’re talking to, and what DNS you’re using, and your VPN provider, and maybe the phase of the moon.
So, pretty much the best-case scenario is when the site works via https, and the server supports “encrypted client hello” (ech), and your browser has ech enabled. In this case your VPN provider can see that you’ve sent something to the IP (one IP can host multiple websites with different domains).
Https and no ech = can see IP, can see the domain.
Http = can see everything (thankfully, quite rare now).
Some VPN providers may as well use their own DNS, then they can see what domains you’ve talked to regardless of ech (afaik, since domain lookup should happen before client hello, since you’re basically looking up whom to “greet”)
Some providers are Facebook with fake mustache and will shamelessly try to mitm you